Cybersecurity Primer - Part II
The Who's Who and What's What breakdown into the key segments within the Cybersecurity theme.
If this is your first time landing on my page, then you may have missed these recent posts, including the first part of this Cybersecurity series:
This is Part II of the Cybersecurity series. With the basics from Part I, it aims to organise the Cybersecurity theme into digestible segments, in which I will drill down at company level later on.
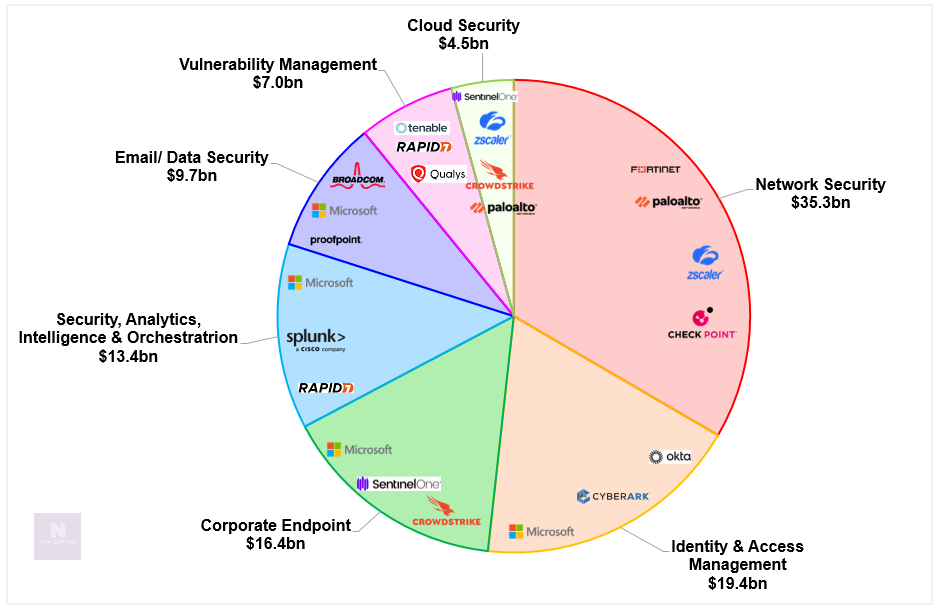
Just to illustrate how wide the theme is, the cheat sheet chart below shows just how many segments there are, and the breadth of players within each segment.
Key Market Segments
The Cybersecurity theme can be split up into the following segments:
Let’s break down each segment in turn.
Network Security
This is the largest segment within Cybersecurity worth $35.3bn.
A network security system, such as a firewall, filters incoming and outgoing network traffic based on pre-set rules to allow/ disallow. The firewall acts as a barrier typically between an internal network and an external, untrusted network (eg. public internet). Back to the castle analogy, the firewall is the locking screen door that lets air in and out (valid requests) but not the mosquitoes (invalid requests).
The Network Security segment is forecast to grow at a 6.1% CAGR to 2027 (Source: IDC) driven by:
new use cases
increasing network traffic
advanced malware protection beyond the basic firewalls offered by the hyperscalers.
The growing adoption of Zero Trust infrastructures has given rise to Firewalls-as-a-Service offerings which disrupt legacy perimeter approaches where firewalls were the first line of defence.
Unified Threat Management (UTM) solutions are a type of firewall that bundle security solutions at a single point in the network - such as intrusion detection/ prevention, URL filtering, and malware protection.
Key players are Palo Alto Networks (27% share), Fortinet (24% share), Cisco (11% share).
Intrusion & Detection Protection (IDP) solutions actively monitor a network for malicious activity, by tracking and analysing activity to block violations. IDP is typically bundled with Firewall/ UTM solutions.
Key players are Cisco (22% share), Check Point (11% share) and Trellix (8% share).
Secure Web Gateway (SWG) protects users’ devices and data from external web-threats whilst the user browses websites. Functions include URL filtering, web content filtering and threat protection. A major growth driver is the increasing need for corporate devices (laptops, mobiles etc).
Key players are Zscaler (30% share), Cisco (15% share) and Broadcom (12% share).
VPN/ Zero Trust Edge allow a company to extend its private network over a public network, to remote offices/ users. This is like a tunnel to allow users to send/ receive data safely on public networks.
Key players are Palto Alto Networks (26% share) and Zscaler (18% share).
Secure Access Service Edge (SASE, pronounced “Sassy”) gives secure access to the network/ cloud applications from anywhere, on any device. It essentially combines firewalls + SWG + IDP into 1 cloud based service.
Key players are Zsclaer (29% share) and Palo Alto Networks (18% share).
Endpoint Security
These solutions protect the endpoints of a network - think desktop computers, laptops, tablets, mobiles, servers etc - from malware and threats. The market is worth $16.4bn and is forecast to grow at a 16% CAGR to 2027 (source: IDC).
Nearly 50% of threats come from the endpoint, so clearly security here is crucial and non-negotiable for any company.
Endpoint Security is the second most prioritised security spend after Idendity & Access Management according to Morgan Stanley surveys. The market is shared by the following players:
Endpoint Security has evolved over time from the original Antivirus Software concept (this reminds me of McAfee Antivirus) that detects computer viruses, to Endpoint Detection & Response software - this detects and contains security incidents and then uses advanced behaviour-based tools, machine learning and AI to combat and anticipate malware.
Identity & Access Management
This is the technology that authenticates users and authorises access. Think multi-factor authentication, single sign on, privileged access management.
The growing adoption of Zero Trust architectures means that identity security becomes a key component of security spend for a company.
The market is worth $19.4bn (source: IDC) currently and Microsoft dominates it unsurprisingly:
Cloud Security
Cloud Security covers cloud workloads, servers, and multi cloud infrastructures. This has gained importance with the rise of AWS, Azure etc becoming more engrained in digital infrastructures.
The key players are Palo Alto Networks and CrowdStrike.
Security Info & Event Management and Analytics
These solutions allow companies to measure and improve their security risk by analysing/ creating/ monitoring the following:
security policies
security logs
responses to alerts
This is a $13.4bn TAM (source: IDC).
As a highly fragmented market, the key players are Splunk (16% share), Microsoft (6% share), IBM (6% share) and DarkTrace (4% share). Many public cloud vendors such as Microsoft Azure and Google Cloud are entering the market, and they have the benefit of a highly scalable cloud platform (and therefore price flexibility) versus stand alone peers.
Vulnerability Management
This is the automated process of identifying, understanding, reporting and fixing weaknesses in code, operating systems and cloud workloads. It is a $7bn TAM (source: IDC).
Key growth drivers include an expanding threat environment and greater cyber regulation.
Most large endpoint and network security players (eg. CrowdStrike, Palo Alto Networks) already embed VM capabilities within their platforms.
Email & Data Security
This is the protection of communication tools including email, instant messaging, social media etc. The solutions defend against malware, phishing, spam, social engineering attacks and unauthorised access. This $10bn market is somewhat mature given that pretty much all enterprises will have adopted this already.
Major players are Microsoft and Proofpoint.
I will deep dive on some key companies within the Cybersecurity theme that I think are interesting longs in my next few posts.
Thanks for reading! As always please let me know your thoughts via the buttons below.